cypherpunks
fyi, the commonmark markup used by lemmy has support for alt text which you aren't using in this post
Oh ffs we’re calling the word “manual” a micro aggression now?
sorry, did my comment trigger you? 🙄
nobody called anything a microaggression or said anything about the non-abbreviated word manual; jokes based on the UNIX's abbreviation of it being homonymous with the common noun man have existed since the man command was created.
nb (short for nota bene) would actually be a good name for a modern replacement for the man command 😂
Wait until you hear about the Alderney pound, Manx pound, Jersey pound, Guernsey pound, Falkland Islands pound, Gibraltar pound, Saint Helena pound, ...
which ones are accepted where is... complicated:
from wikipedia:
Throughout the UK, £1 and £2 coins are legal tender for any amount, with the other coins being legal tender only for limited amounts. Bank of England notes are legal tender for any amount in England and Wales, but not in Scotland or Northern Ireland.
[...]
Bank of England, Scottish, Northern Irish, Channel Islands, Isle of Man, Gibraltar, and Falkland banknotes may be offered anywhere in the UK, although there is no obligation to accept them as a means of payment, and acceptance varies. For example, merchants in England generally accept Scottish and Northern Irish notes, but some unfamiliar with them may reject them.[142] However, Scottish and Northern Irish notes both tend to be accepted in Scotland and Northern Ireland, respectively. Merchants in England generally do not accept Jersey, Guernsey, Manx, Gibraltarian, and Falkland notes but Manx notes are generally accepted in Northern Ireland.[143] Bank of England notes are generally accepted in the Falklands and Gibraltar, but for example, Scottish and Northern Irish notes are not.[144] Since all of the notes are denominated in sterling, banks will exchange them for locally issued notes at face value,[145][failed verification] though some in the UK have had trouble exchanging Falkland Islands notes.[146]
🤡
the edit history on Shehbaz Sharif's tweet shows that it began with "Draft - Pakistan's PM Message on X" when it was first posted 😭
certain 2-parters are counted as 1
this explains the total of 170
a handful are credit only
as a main cast member he is in the opening credit sequence of every episode, which explains IMDB saying he's in every one.
but how/where did you arrive at the number 163? i only arrived there by seeing that Memory Alpha lists 160 character appearances (which I see now does single-count Emissary and presumably two other two-part episodes) and then checking the mirror universe episodes to see if there were any without the Chief in them (and finding two) and then remembering Far Beyond the Stars.
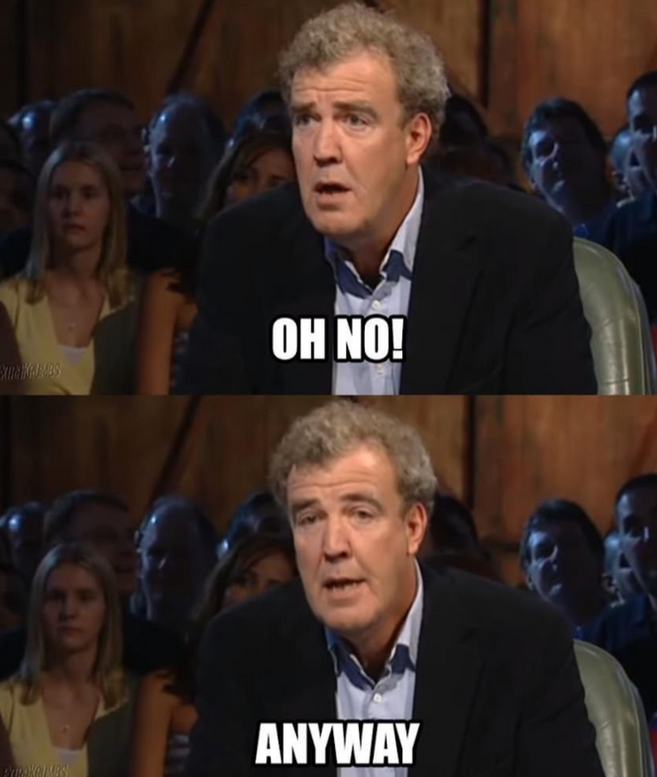
anyway i guess either of the numbers in the meme could be correct, but not both at once: 163 is correct if you double-count three two-part episodes, and 170 is correct if you single-count them. 🤓
(and the numbers in my first comment are inconsistent in the same way.)
Fucking Chief Miles O'Brien appeared in 163 of 170 episodes, Dude

For one thing, there were 173 episodes of DS9.
And while Colm Meaney does appear in 163 of them, he is only portraying Chief Miles O'Brien in 160 episodes: in Far Beyond the Stars he portrays Albert Macklin and in The Emperor's New Cloak and Through the Looking Glass he portrays mirror universe Miles O'Brien.
I am curious where the creator of this meme arrived at the number 163, since IMDB incorrectly says that Meaney is in all 173 episodes.
ps:
good meme nonetheless
thanks, i edited the post to link that instead



😬
That website is made by someone suffering from some cognitive dissonance. They correctly observe that LLMs "can produce convincing-sounding information, but that information may not be accurate or reliable" but then somehow immediately afterwards conclude that "summarize this for me" is the type of thing which LLMs "might" be "good at".