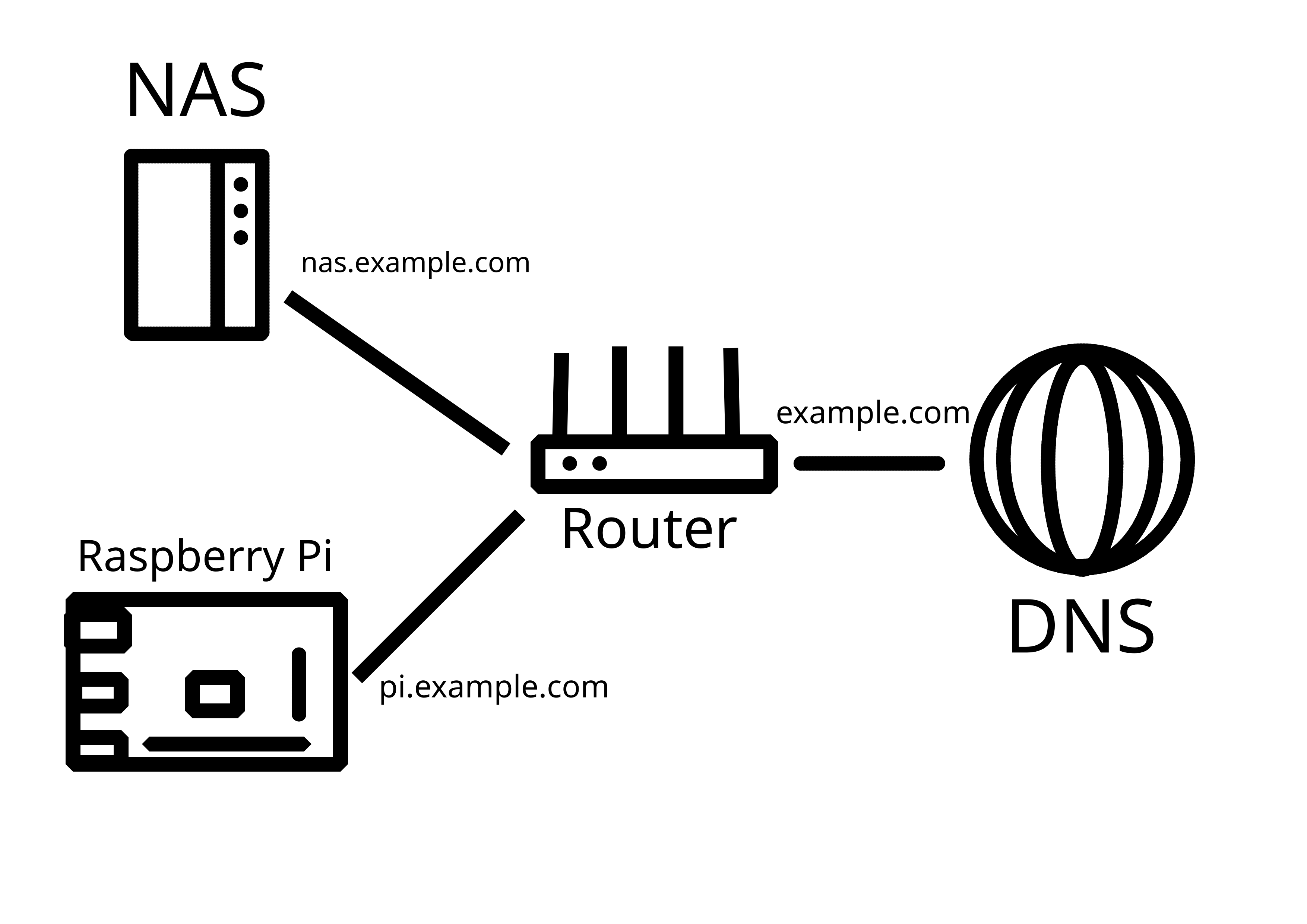
You need a reserve proxy. That's a piece of software that takes the requests and puts them toward the correct endpoint.
You need to create port forwards in the router and direct 80 and 443 (or whatever you're using) toward the host of the reverse proxy and that is listening to on those ports. If it recognized the requests are for nas.your.domain, it will forward the requests to the NAS.
Common reverse proxies are nginx or caddy. You can install it on your raspberry, it doesn't need it's own device.
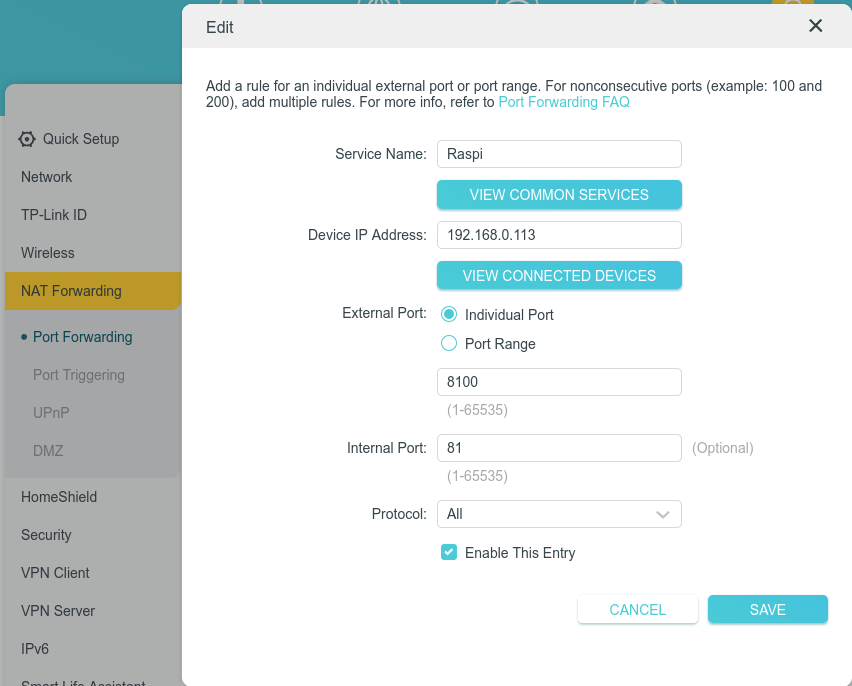
If you don't want that, you can create different port forwards on your router (e.g. 8080 and 8443 to the Raspi) and configure your service on the Raspi corresponding. But it doesn't scale well and you'd need to call everything with the port and the reverse proxy is the usual solution.