news
Welcome to c/news! We aim to foster a book-club type environment for discussion and critical analysis of the news. Our policy objectives are:
-
To learn about and discuss meaningful news, analysis and perspectives from around the world, with a focus on news outside the Anglosphere and beyond what is normally seen in corporate media (e.g. anti-imperialist, anti-Zionist, Marxist, Indigenous, LGBTQ, people of colour).
-
To encourage community members to contribute commentary and for others to thoughtfully engage with this material.
-
To support healthy and good faith discussion as comrades, sharpening our analytical skills and helping one another better understand geopolitics.
We ask community members to appreciate the uncertainty inherent in critical analysis of current events, the need to constantly learn, and take part in the community with humility. None of us are the One True Leftist, not even you, the reader.
Newcomm and Newsmega Rules:
The Hexbear Code of Conduct and Terms of Service apply here.
-
Link titles: Please use informative link titles. Overly editorialized titles, particularly if they link to opinion pieces, may get your post removed.
-
Content warnings: Posts on the newscomm and top-level replies on the newsmega should use content warnings appropriately. Please be thoughtful about wording and triggers when describing awful things in post titles.
-
Fake news: No fake news posts ever, including April 1st. Deliberate fake news posting is a bannable offense. If you mistakenly post fake news the mod team may ask you to delete/modify the post or we may delete it ourselves.
-
Link sources: All posts must include a link to their source. Screenshots are fine IF you include the link in the post body. If you are citing a Twitter post as news, please include the Xcancel.com (or another Nitter instance) or at least strip out identifier information from the twitter link. There is also a Firefox extension that can redirect Twitter links to a Nitter instance, such as Libredirect or archive them as you would any other reactionary source.
-
Archive sites: We highly encourage use of non-paywalled archive sites (i.e. archive.is, web.archive.org, ghostarchive.org) so that links are widely accessible to the community and so that reactionary sources don’t derive data/ad revenue from Hexbear users. If you see a link without an archive link, please archive it yourself and add it to the thread, ask the OP to fix it, or report to mods. Including text of articles in threads is welcome.
-
Low effort material: Avoid memes/jokes/shitposts in newscomm posts and top-level replies to the newsmega. This kind of content is OK in post replies and in newsmega sub-threads. We encourage the community to balance their contribution of low effort material with effort posts, links to real news/analysis, and meaningful engagement with material posted in the community.
-
American politics: Discussion and effort posts on the (potential) material impacts of American electoral politics is welcome, but the never-ending circus of American Politics© Brought to You by Mountain Dew™ is not welcome. This refers to polling, pundit reactions, electoral horse races, rumors of who might run, etc.
-
Electoralism: Please try to avoid struggle sessions about the value of voting/taking part in the electoral system in the West. c/electoralism is right over there.
-
AI Slop: Don't post AI generated content. Posts about AI race/chip wars/data centers are fine.
view the rest of the comments
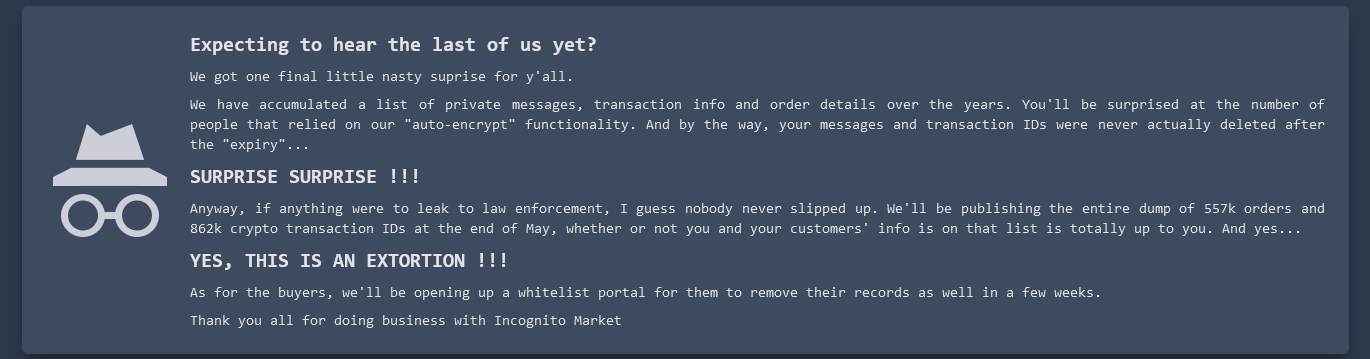
Vendors I think have the ability to deny customers for whatever reason they want and vice versa. If you're a buyer and your vendor refuses to use PGP, you should find another vendor. If you're a vendor and your buyer refuses to use PGP you should simply block them and not vend to them. I'm also getting the impression that this wasn't common practice on Incognito, but years ago back when I, um, read about this stuff, it was never a majority but it wasn't uncommon for vendors to state up front they only vend to people who will use PGP. Sometimes vendors would give a discount to people who did. I'm sure a lot of vendors right now are wishing they had followed that very common sense policy.
I edited this comment for clarity and because I accidentally said something backwards initially:
Hmm, it should be plainly obvious if someone is encrypting their messages to you. Like, what I think you're describing couldn't even work by accident. Other people's keys can't be used. If someone wants to communicate with you, they need your public key to encrypt their message to you and only you can then decrypt that message with your private key. If you then want to respond, you need their public key to encrypt your response, which only they can decrypt.
Example: if a buyer contacts a vendor, the buyer is not using their (the buyer's) own key. The buyer must use the vendor's public key to encrypt a message that the vendor then decrypts locally (which only the vendor can do with their private key). If the buyer used any other key, the vendor couldn't decrypt the message and no transaction could proceed. If the vendor wants to then send a message to the buyer, that's when the vendor uses the buyer's public key to encrypt that message. If the buyer gave the vendor any public key that is not their own, that buyer then couldn't decrypt the message the vendor sent them. There's really no place in this process where the vendor wouldn't know if the buyer was using their own PGP key.
In my past experience, people would put their public keys in their profile. The auto-encryption doesn't even look like encryption, it just looks like sending messages normally, the same way it looks using any encrypted messenger service: you just accept and trust that the service really is encrypting and decrypting at both ends and all you see is the text that someone sends you. There are steps both you and the person you're talking to have to take when doing your own encryption. Even when you're using PGP, you're still sending text over the market messaging system, and the market is encrypting that, but the text you're sending will look like total gibberish to everyone. Not just to the market, but it will look like total gibberish even to you after you encrypted the text locally on your own device, and of course it will also look like total gibberish to the person you're sending it to until they decrypt it locally on their end. There really should be no room for confusing who's public key is being used, not even mistakenly because the decryption wouldn't work. Unless I'm still misunderstanding you, or unless communication methods on the DNMs have so drastically changed in recent years that they're incomparable, but I know that's not the case.