Thanks for warning. Saw https://monero.town/post/872283 too. Guess Cake Pay may be convenient for those who are fine with KYC. Another option, that Stealths thing is more expensive (higher fees), so basically if you want to buy a gift card here or there, you’ll have to choose between (possible) KYC and higher fees. Or so it seems…
According to @azalty@monero.town, Cake Pay works fine if you’re fine with KYC, and otherwise you may just lose your money: https://monero.town/post/872283
If you’re a privacy advocate not fully supporting KYC but want to try this anyway, then try a small amount, because you may lose all your money. Another recent option is more privacy-friendly and KYC-free, but the fees are higher with them.
We know the ability to get Monero will not be essentially affected—after all, this is not the first time, nor the second time, when Monero is delisted. It seems reasonable to admit, though, that ultimately the ability/freedom to spend Monero might be limited if legit (e.g. hosting) companies can’t accept it in the future—directly or indirectly because of MiCA etc. Although, what will happen in such a situation may be seen as an interesting experiment.
Since the posted link is not very Tor-friendly behind CF, similar random links just in case…
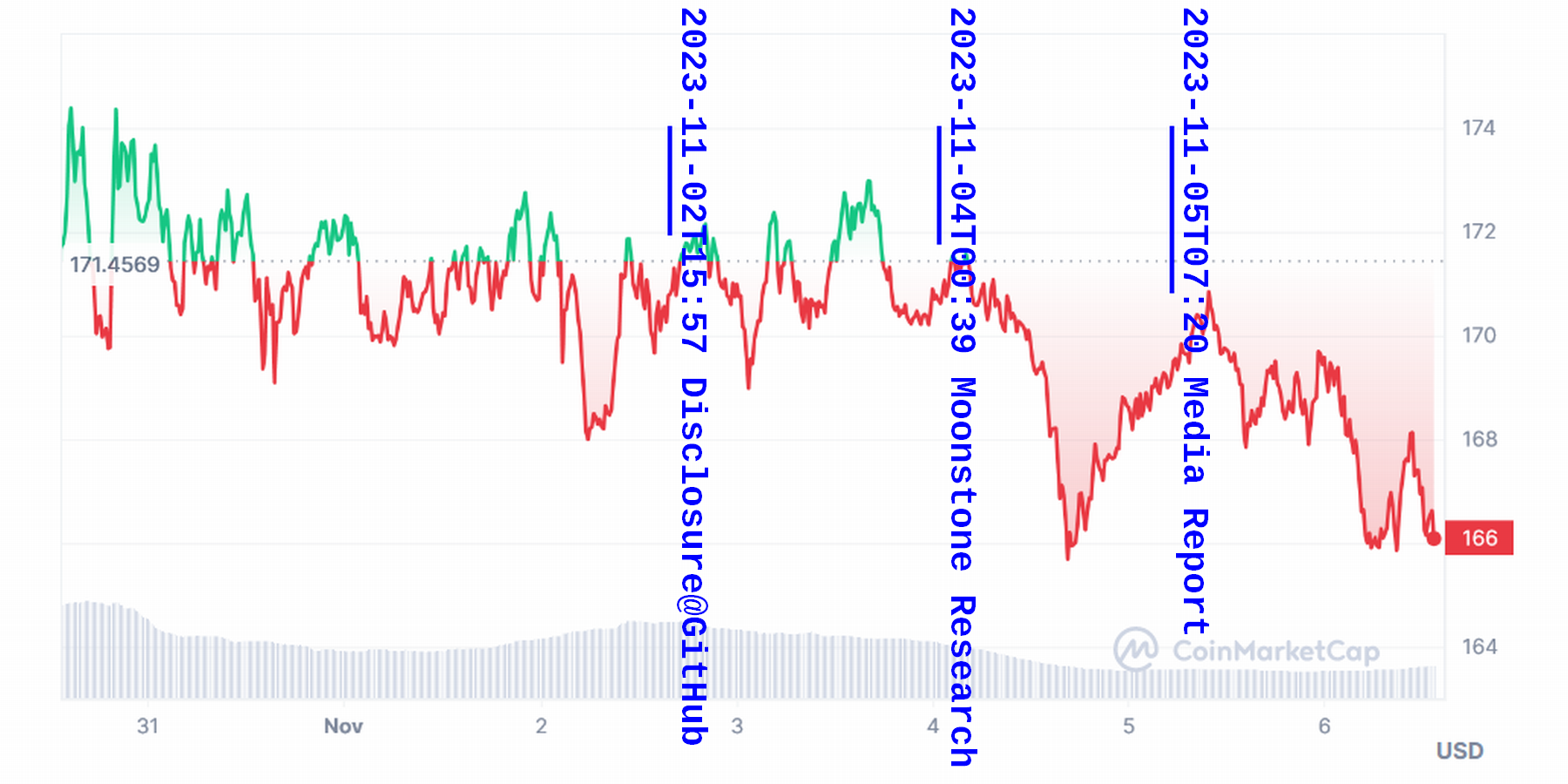
- OKX exchange delists privacy coins, including Monero, Dash, and Zcash https://www.cryptopolitan.com/okx-delists-privacy-coins-monero-dash-zcash/
Following the announcement, privacy tokens such as Dash (DASH), Monero (XMR), and Zcash (ZEC) witnessed a notable decline of up to 10%
- Important OKX Delisting Announcement Concerning Large Subset of Altcoins https://cryptopotato.com/important-okx-delisting-announcement-conrcening-large-subset-of-altcoins/
The prices of some of these tokens have headed south shortly after the announcement. XMR is down nearly 3% in the past 24 hours, while ZEC has plunged by 10%
- Crypto Exchange OKX All Set to Delist Privacy Coins https://thenewscrypto.com/crypto-exchange-okx-all-set-to-delist-privacy-coins/
- Zcash and Monero on the chopping block for delisting https://www.cryptopolitan.com/naira-is-about-to-have-its-worst-year-ever/
The concept may be lovely, but the fact is, many people nowadays have been Pavlov’ed to immediately ignore anything weird that says, "Congratulations! You got some money. Visit this URL and input something." As they say, the Cake is a lie…
Monero could be a wonderful gift to a friend of yours if they’re especially interested in privacy (in that case, you might want to talk to them privately, and perhaps recommend a better wallet). Otherwise, it may be kind of like casting pearls before swine…
Trocador shows it explicitly whether a specific CEX is no-log or requiting IP logging, which you can choose. This new thing doesn’t have TOS nor Privacy Policy to begin with. Yet as long as you use onion, logging by the front-end is rather irrelevant.
Even if the front-end is not logging anything (which no one can verify), a CEX behind it surely records the tx and retains it as required by laws (some of them might be less than perfectly legal and might not record anything, though that would mean a different kind of risk). Using a CEX is more or less risky, be it Trocador or something else. Some may think that an instant swap by CEX is convenient. Personally I prefer DEX, even though it may be less convenient, even though Monero.town itself has an official affiliate link to Trocador too.
Asia might potentially be a better idea (not Japan or Korea though)
You mean, like Hong Kong, or India, maybe? What do you mean by “not Japan or Korea though”? I’d feel China would be worse. Privacy-focused services tend to be pricey anyway, both in Europe and in the US, and the price comparison is tricky as EUR/USD can move weirdly. If you’re talking about Njalla (Sweden), it’s indeed rather expensive.
Although France seems to be generally anti-cryptography, of course you wouldn’t go to jail just because you use Tails. There was this notorious incident related to French activists & Proton, though. Also, the Netherlands can be scary. They arrested a developer of Tornado Cash, right? Although, those things have nothing to do with VPS!
Thank you so much! These minor details are really helpful :D Happy holidays!
It’s true that the EU is getting “difficult”. Ironically, the US (without GDPR) can be better, where the right to anonymous speech is more or less protected (although, of course, US hosting companies in general are not good for that).
IncogNet is a good example, where you can get a domain anonymously, just like from Njalla but the price being much affordable. Not only that, they’ll set up an onion/I2P version for your website for free. (This is not a recommendation, though. DYOR.)
Floki was once famous but, yeah… they’re getting a bit less popular now after the Covid things. It’s not Iceland and Seychelles based; basically it’s a German company, having servers in Iceland, Finland, Romania, and the Netherlands. Iceland was once very popular, but anymore. Using a .is domain now assuming it’s “safer” is a bit yesterday.
Especially, be aware of France: they’re like “you use encryption because you have something to hide, doing something bad.” Also, you might want to avoid EU domains (.fr etc.) in general: check about NIS2, so called “Thick Whois“ to see what this means. For example, you can’t get a .nl anonymous domain anymore (a recent change); a similar trend being expected soon in other EU registrars/resellers i.e. “domain KYC”.
PS: Incognet is based on Fran's (Frantech/BuyVM) in Canada, which has been generally trusted and has some good track record. One might want to consider BuyVM etc. too (Not a recommendation, DYOR).
PPS: Incognet accepts xmr, but you can’t do crypto-related things like mining on their servers. A negative point for some of us.
Exactly how does you activate it? Ordering itself is kyc-free (and even Tor-friendly?) but you’ll need to show your IP to activate it, of course?
@stealths@monero.town Thanks for clarification!
- For example, a user in China can buy a card from you, redeem (activate) it and use it internationally, except they can’t use it in shopping at an online shop China?
- A user in Pakistan can not activate it and use it at all, though others can use it for shopping internationally incl. at at online shop in Pakistan.
It that what this means? I assume activation then includes GeoIP? I’m very happy that a few user reviews are positive anyway. You know, some “services/companies” advertising here tend to be a bit sketchy or iffy. Your prepaid card business seems a honest one, at least now! Thanks for joining monero.town :) I hope this can be convenient & fruitful for both users and you 🐱
Visa International (Just fyi): The supported country list by Stealths and the similar list by Tremendous are slightly different. The differences (if real) might be mostly relevant to Chinese users.
These three are included in Stealths’ list, but not included in Tremendous’ list:
China, Hong Kong (*Taiwan is in both lists), Swaziland
These countries/areas are not inluded in S’s list, but are included in T’s list:
Bosnia and Herzegovina, Burundi, Congo (*Flag of Congo-Brazzaville is shown), Eswatini, Pakistan, Panama, Saint Helena, Saint Pierre and Miquelon

So perhaps your recent bad experience with Mastercard EUR cards are rather exceptional?