All the cool projects I see while lurking around here have thrown me into the world of Self-Hosting! Some months ago I got myself a NAS, flashed it with TrueNAS and started playing. Today, I am ready to face the creation of my first homelab.
Since I got the basic data storage working, I decided to continue with the Firewall setup. I’d like to have my security figured out before I start spinning up machines, playing with their configs and unwittingly opening all kind of arcane doors to the unknown. So I turn to the Fediverse!
I’d like to create the standard network with a DMZ. Within the network, I plan to use VLANS to manage traffic between devices, and the firewall to limit internet access.
This is a sketch of what I think I want to achieve:
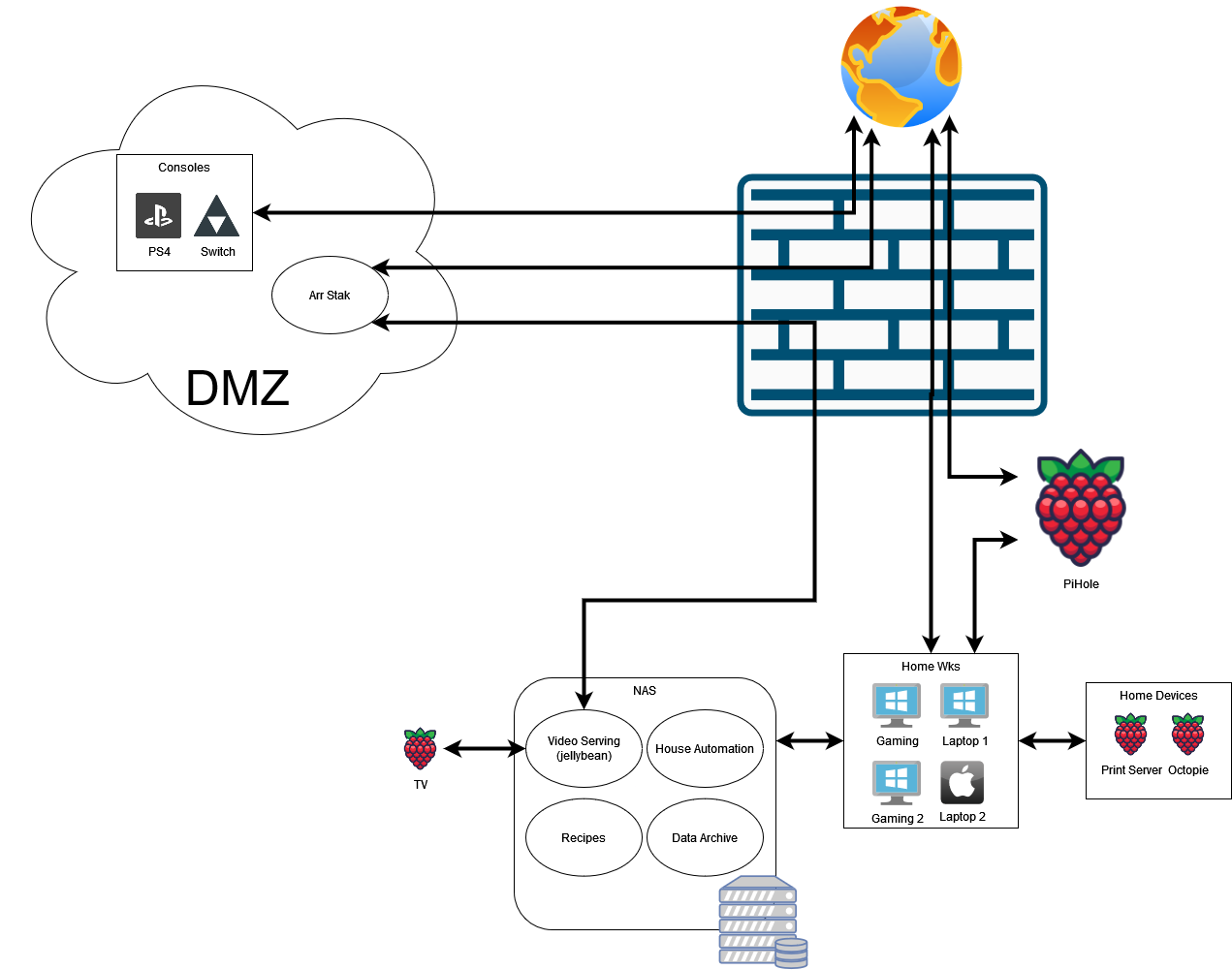
Connections
- The Consoles will connect only to the internet
- The Home Devices (printers) will connect only to the Home WKS
- There will be a NAS device hosting VMs with services accessible only from the home network:
- The Home Automation will connect to IoT
- The Recipes will connect to Home Wks
- The Data Archive will connect to Home Wks
- Jellybean will connect to:
- Home Wks
- TV
- *arr Stack will connect to:
- The Internet
- the NAS (presumably Jellybean)
- The Home WKS connect to pretty much anything
Available Hardware
- OpenWRT compatible Router
- 2.5gbs Unmaged Switch
- 1gbs Unmaged Switch
- QNAS with 2x2.5gbs NIC, running TrueNas
- A few Rpis of different specs
Questions
Firewall
My Main questions relate to the Firewall. It seems that pfsense is the way to go for a SW Firewall:
- What HW should i use? would a Raspberry pi 4, 4GB RAM work?
- What do you think of Netgear 1100?
- I like this device since 3ports would allow me to create a physically separate DMZ
- Should I consider other firewalls?
NAS
For Bonus Points, some questions regarding the NAS:
- With my current diagram, it seems like it is not possible for the NAS to receive updates from the internet. The obvious change is to place the NAS within the DMZ, but I’d like to keep the Data Archive as far from the net as possible
- Should i locate the entire NAS in the DMZ?
- My TrueNas has 2x2.5Gb ports. Can i connect each NIC to a different network? Would this have any benefit?
Thanks for your time!
I do tend to overcomplicate things 😆
It seems, based on your comments and others in the post, that my next step is to flash OpenWRT and do a deep dive on its firewall functions. Thanks for taking the time to educate me!
Yeah - basic home-networking is typically pretty straight-forward. You'll want to figure out your basic services (DHCP, DNS, and routing) but after that it's pretty simple. OpenWRT should handle the DHCP and routing. I'm not sure about DNS though.
DHCP will tell systems "here is your IP, here is the CIDR of the network you are on, here is the router that handles traffic for things NOT on that network (e.g. the internet), and here are the DNS servers you should use for name resolution.
With DHCP you can also hand out "static leases" to give systems reliable IP addresses based on their MAC addresses. Then you can setup a DNS server that does internal name resolution if you want to be able to reference systems by name. This DNS server doesn't need to be publicly available (and indeed should not be).
The Firewall is typically only for things coming into your network from the internet. You can restrict outbound traffic as well if you want but that's less common. By default things on the internet will NOT be able to get to your internal systems because of NAT. So to allow things "out there" to access a service running on an internal system you'll need to do port forwarding on your firewall. This will a) open a port on the internet side and b) send all traffic to that port to a port on an internal system. The router will handle all of the network-to-network and traffic handling stuff.
I’ll make a note here that a firewall is useful for internal traffic, too. Those IoT devices can get pretty annoying, so you'd want to e.g. drop your cheap webcams into a VLAN and disallow them from talking to enjoying but their cloud, and especially the other VLANs, or isolate Alexa capable device so it won’t try to figure what else you got there in your house over mDNS (it will).
A managed switch would do nicely. Having isolated ports on the switch (and the wifi AP) is also great if you want to make sure the specific device will only talk to the gateway and not its peers.