this post was submitted on 04 Mar 2026
530 points (98.7% liked)
Programmer Humor
30962 readers
1446 users here now
Welcome to Programmer Humor!
This is a place where you can post jokes, memes, humor, etc. related to programming!
For sharing awful code theres also Programming Horror.
Rules
- Keep content in english
- No advertisements
- Posts must be related to programming or programmer topics
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
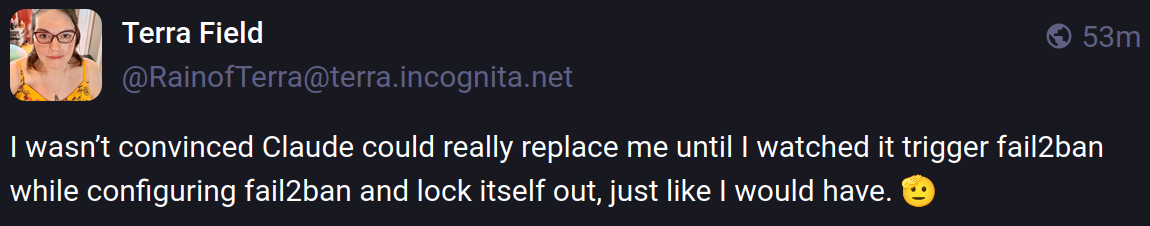
this seems like something I would do too, which is why I haven't installed fail2ban
You should really install fail2ban, juat for peace of mind. If you dont, at the very least setup SSH keys.
I was making a joke. I already have rate limiting protecting my Authelia login page.
unless I have an insecure password or a security vulnerability in sshd, how would it be a problem? I haven't had any issues for the last 6 years.
You mean key based SSH authentication? Yes, but if you have done so and this is the only attack vector, I do not see the need for fail2ban.
I set up, and prefer, iptables rules to rate limit logins.
I have mine set so you can connect up to 5 times per 15 minutes.
Blocks bots well enough, and if I really mess up, I just wait 15 mins
The nice thing about SSH key-based access is, I either have the key and login succeeds, or I have no business trying to log in.
That's why my remote root server bans via fail2ban after a single failed login.
Yes I've had to write support to get a KMS. Yes it's still configured like this.
i am a tailscale enjoyer, which means i can set up tailscale ssh once on each machine and then from another machine just login over tailscale
Eh, the machine is actually in one of my wireguard nets anyways, but for different purposes.
How's that different from normal ssh?
you can disable the need for a password or key if you like, and you also don't really need fail2ban, since nothing is actually port forwarded anywhere
as a nixos enjoyer, i have no idea how to setup ssh keys. fail2ban and a regular password for me.
yes, i have locked myself out of my own server for hours at a time because i'm an absolute tool.
Ehm... I'm also on Nixos and I'd say it's super trivial.
So easy it should be illegal! I mean, how can we feel superior if we are not wasting huge amounts of time setting things up!?
Why, by boasting that it's so easy, just look at that, it is only two options you need to set thanks to the 80 custom modules I've written to abstract the abstractions from nixpkgs!
I WISH I could put an /s here, but I cannot.