Games

Welcome to the largest gaming community on Lemmy! Discussion for all kinds of games. Video games, tabletop games, card games etc.
Rules
1. Submissions have to be related to games
Video games, tabletop, or otherwise. Posts not related to games will be deleted.
This community is focused on games, of all kinds. Any news item or discussion should be related to gaming in some way.
2. No bigotry or harassment, be civil
No bigotry, hardline stance. Try not to get too heated when entering into a discussion or debate.
We are here to talk and discuss about one of our passions, not fight or be exposed to hate. Posts or responses that are hateful will be deleted to keep the atmosphere good. If repeatedly violated, not only will the comment be deleted but a ban will be handed out as well. We judge each case individually.
3. No excessive self-promotion
Try to keep it to 10% self-promotion / 90% other stuff in your post history.
This is to prevent people from posting for the sole purpose of promoting their own website or social media account.
4. Stay on-topic; no memes, funny videos, giveaways, reposts, or low-effort posts
This community is mostly for discussion and news. Remember to search for the thing you're submitting before posting to see if it's already been posted.
We want to keep the quality of posts high. Therefore, memes, funny videos, low-effort posts and reposts are not allowed. We prohibit giveaways because we cannot be sure that the person holding the giveaway will actually do what they promise.
5. Mark Spoilers and NSFW
Make sure to mark your stuff or it may be removed.
No one wants to be spoiled. Therefore, always mark spoilers. Similarly mark NSFW, in case anyone is browsing in a public space or at work.
6. No linking to piracy
Don't share it here, there are other places to find it. Discussion of piracy is fine.
We don't want us moderators or the admins of lemmy.world to get in trouble for linking to piracy. Therefore, any link to piracy will be removed. Discussion of it is of course allowed.
Authorized Regular Threads
Related communities
PM a mod to add your own
Video games
Generic
- !gaming@Lemmy.world: Our sister community, focused on PC and console gaming. Meme are allowed.
- !photomode@feddit.uk: For all your screenshots needs, to share your love for games graphics.
- !vgmusic@lemmy.world: A community to share your love for video games music
- !freegames@feddit.uk: A community sharing free games giveaways.
Help and suggestions
By platform
By type
- !AutomationGames@lemmy.zip
- !Incremental_Games@incremental.social
- !LifeSimulation@lemmy.world
- !CityBuilders@sh.itjust.works
- !CozyGames@Lemmy.world
- !CRPG@lemmy.world
- !horror_games@piefed.world
- !OtomeGames@ani.social
- !Shmups@lemmus.org
- !space_games@piefed.world
- !strategy_games@piefed.world
- !turnbasedstrategy@piefed.world
- !tycoon@lemmy.world
- !VisualNovels@ani.social
By games
- !Baldurs_Gate_3@lemmy.world
- !Cities_Skylines@lemmy.world
- !CassetteBeasts@Lemmy.world
- !Fallout@lemmy.world
- !FinalFantasyXIV@lemmy.world
- !Minecraft@Lemmy.world
- !NoMansSky@lemmy.world
- !Palia@Lemmy.world
- !Pokemon@lemm.ee
- !Silksong@indie-ver.se
- !Skyrim@lemmy.world
- !StardewValley@lemm.ee
- !Subnautica2@Lemmy.world
- !WorkersAndResources@lemmy.world
Language specific
- !JeuxVideo@jlai.lu: French
view the rest of the comments
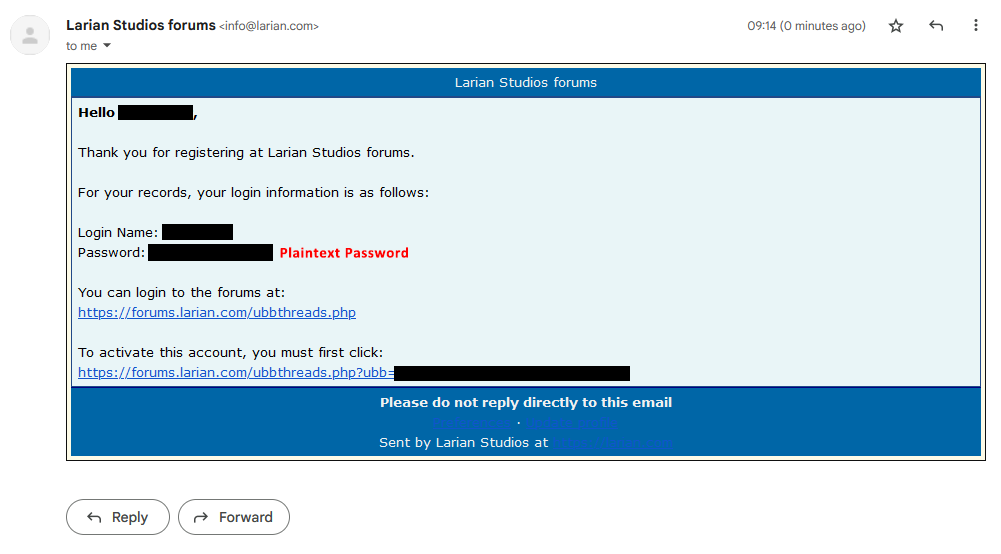
Maybe I'm misunderstanding you, but backend servers will almost always have the user-submitted password in plaintext as a variable, accessible to the backend server and any upstream proxies.
It's even how it's done in Lemmy. The bcrypt verify accepts the plaintext password and the expected salted hash.
There are ways to have passwords transmitted completely encrypted, but it involves hitting the backend for a challenge, then using that challenge to encrypt the password client side before sending. It still gets decrypted on the backend tho before hash and store.
Yeah, but SSL/TLS also solves that problem in a standardized way.
In either case, the backend will have the plaintext password regardless of how it's transmitted.
Yes, which is why they're vulnerable to mitm and local sniffer attacks.
Have you found a mitm attack on TLS?
This guy's a fucking clown, I'm sure he's like 15
Not without compromised certificates they haven't. You can tell because if they did they'd be world famous for having destroyed any and all internet security. Then again, they'd probably already be famous for having figured out a way to salt, hash and store passwords without ever holding them in memory first like they claim to do above, so maybe someone is lying on the internet about their vague "proprietary network protocols".
Oh yeah, this guy is a hoot.
I haven't looked into it but I was wondering about the logistics of setting up a federated honeypot for server side stream sniffing to build a plaintext email/password database.
Man, you sound like you're just using random words you heard in class. Clearly you have no clue how user registration actually works, let alone backend development.
Well it's a good thing your opinion has no effect on reality.